Recently in the March 2018 security bulletin, a fix was released to address the CredSSP Encryption Oracle Remediation vulnerability. The problem with this fix was that if you are running Azure VM’s in your environment that are not up and running on a regular basis they may not have received the fix. I hear you say, what is the problem with that? Well if you apply the patch to you workstation or laptop and the vulnerability patch has not been applied to your azure VM then you can not rdp to your azure vm.
Yes this is a problem. However there is a workaround to allow you to still have access to your azure vms and stay safe.
- If you have access to a workstation or laptop that has not yet been updated, then from this workstation or laptop, RDP to your Azure vm and ensure all recent and uptodate patches are applied.
- If step 1 is not available you can still gain access with undertaking the following steps in this post. That said, this does open you up to some potential risk so you need to ensure your safety before proceeding. The advice in this post is a guide and you need to ensure you follow all of your own security requirements to proceed.
The first step in being able to access your Azure servers from a workstation or laptop that has already been patched is:
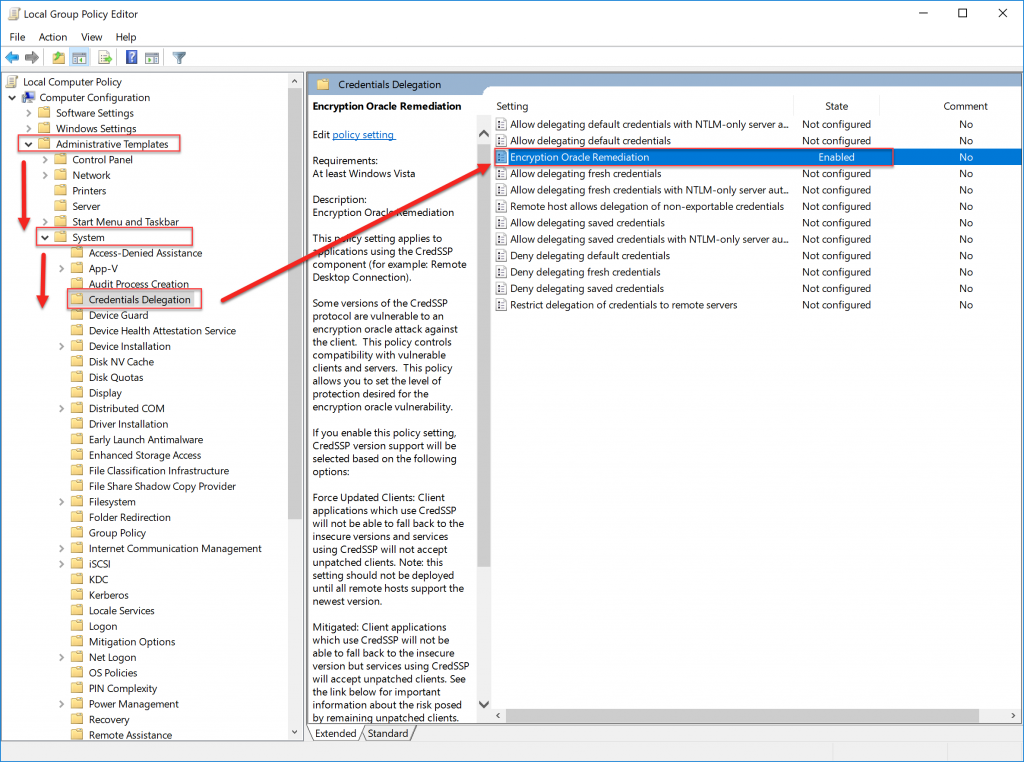
- Open Group Policy Editor. Hit your start key | type gpedit.msc
- Navigate to Administrative Templates | System | Credentials Delegation
- Select Encryption Oracle Remediation
- Click Edit
- Select Enabled
- Select Protection Level – Vulnerable
- Click Ok
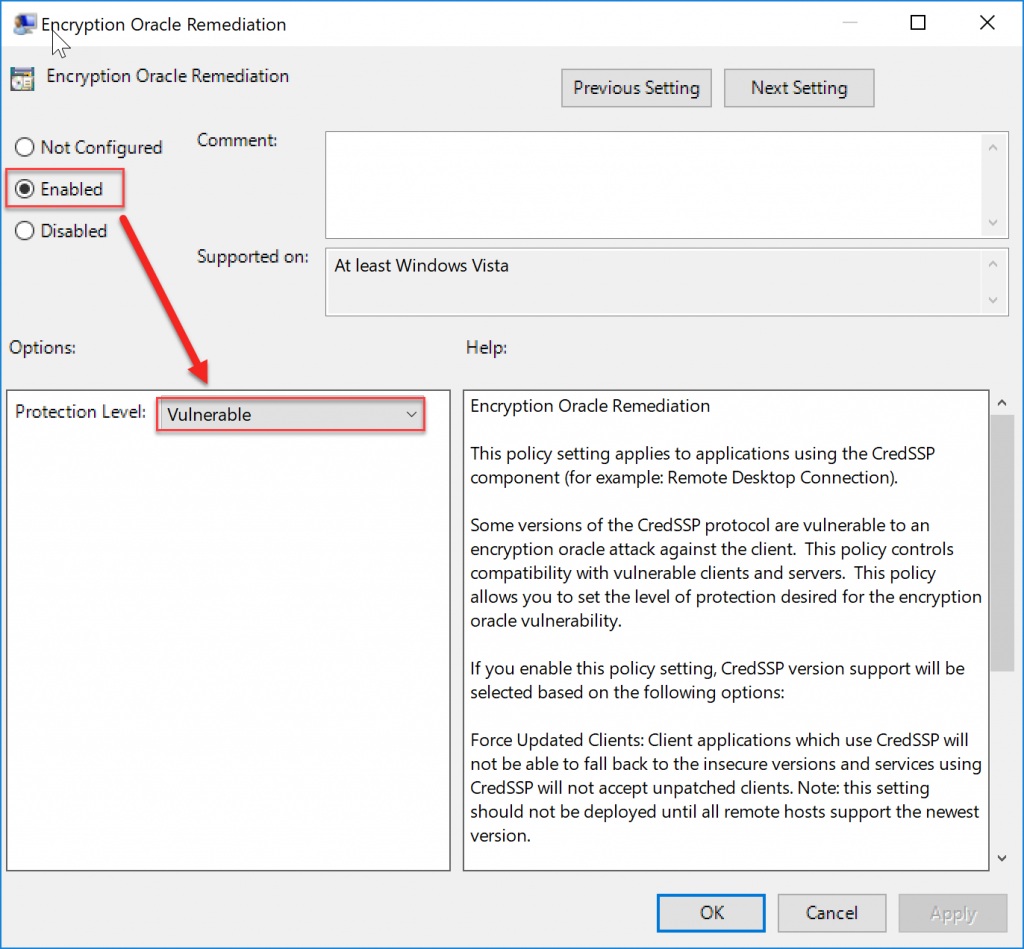
You can now RDP to your Azure VM and download and install the most up todate patches. Remember, once you have done this to return you Credentials Delegation back to the original required settings. This technet blog article helped in putting this post together.
Make sure that you reverse the steps you followed above to ensure that your workstation or laptop is no longer in a vulnerable or compromised position.
I hope this helps.







Leave a Reply